Do you know
-what data you have?
-where your data is stored?
-who is touching your data?
-what they do with your data?
If you’re struggling to answer those questions, you can rest assured that you are not alone. Staying on top of all the data we now generate is becoming more difficult than ever.
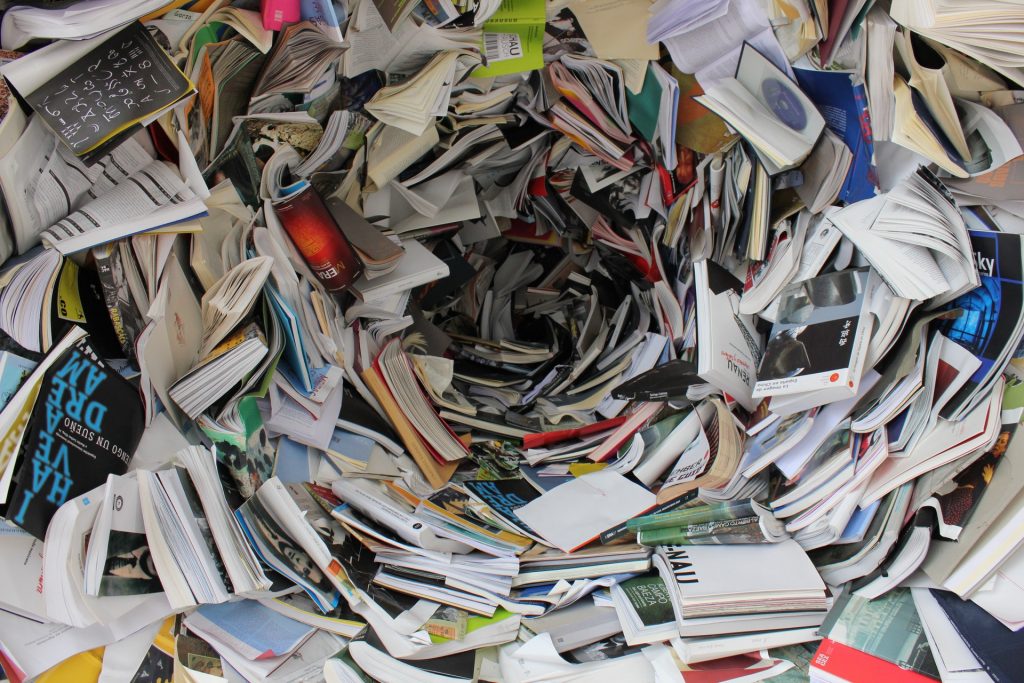
Knowing the nature of that data, where it is, and who is accessing it, is knowledge that is sadly lacking in many organisations. This can lead to security failures such as data leaks and data breaches, both malicious and inadvertent. In turn, these failures can do great damage to a company’s reputation and financial wellbeing. This damage can take a long time to repair…if it can be repaired at all.
Here’s a stark reminder of how much harm can be done following a data breach. Australian businesses take, on average, 200 days to identify a data breach, and a further 81 days to contain it. This all comes at a price. In 2018-2019, the average cost of a data breach to an Australian business rose to more than $3 million. This might include compensating affected clients, paying for the breach response e.g. setting up a helpline for affected clients, hiring an outside party to investigate the breach, a fall in share prices, or having to pay (harsh) regulatory penalties.
The vast majority of businesses couldn’t wear a cost like that, yet that’s not the only extreme pain point. Any security breach has a reputational cost as well, and consumer choices will be made accordingly. People might simply choose to deal with companies that can securely manage the sensitive information they provide to them.
When data is not understood, respected or protected, a security failure is more than a possibility, it’s a probability. In the current climate where we’re producing bamboozling amounts of hard-to-manage data, it could even be considered an inevitability, whether it’s from an external attack, or an inadvertent mistake from an employee.
The more data we make, the more challenges we face
Businesses are generating more data than ever before: it has been estimated that more than two quintillion bytes of data are created around the world each day. That’s 2,000,000,000,000,000,000,000 bytes of data created every single day!
Within all this data is valuable information that can help organisations do better business through sharper decision making, personalised marketing, better inventory control, and enhanced customer service, all of which are based on using data in a smarter way. But as the amount of data increases, so does the challenge in managing it, and securing it.
Traditional information governance is old news
Much of the data an organisation stores, consists of highly sensitive information about their customers. Names, addresses, credit card details, credit history, bank account numbers, medical history, family information, and even religious and political beliefs: things like this are rightly seen as confidential and private. Yet, for a transaction to be made, customers concede that this sensitive information has to be passed on to the company they’re dealing with.
They might do so with a fair degree of trepidation, but also with an obvious expectation that their information will be treated securely, and with respect. They place a good deal of faith in the organisation’s information governance: the policies, procedures and processes surrounding information management, as well as the security model that keeps this information safe and confidential.
Unfortunately, an organisation that doesn’t understand or value the true worth of data can’t be relied upon to provide an information governance framework that is robust and secure, and this penalises both the company and the customer.
This is especially true when their information governance policies and procedures reflect a bygone era, and haven’t been updated to adequately protect today’s massive, and ever growing, data stores. They leave themselves open to external attacks and they fail to look closer to home and recognise the need to guard sensitive information from those on the inside: more than 60% of data breaches are as a result of intentional or inadvertent actions by employees.
While data breaches from external attacks tend to make headlines, the fact of the matter is that many data security failures are accidental, and are caused by a company’s employees. These inadvertent breaches could be caused by things as simple as sending an email or a piece of correspondence to the wrong address, unintentional posting of information, or losing a laptop or mobile phone. That doesn’t make the breaches any less harmful, of course, but it underlines the need for a strong data culture with complete buy in from everyone in the organisation, from the board level to the most junior staff.
While accidents happen, a company, where data is respected, as much as the customer’s right to privacy would see the instances of inadvertent breaches reduced: email and postal addresses would be doublechecked so that the right thing reaches the right person, or a device would be valued much more highly so that it is always in sight of the person charged with looking after it. It’s not much to ask is it?
Of course, it goes deeper than that. If we go back to the questions we asked at the start of this article, many organisations also leave themselves open to malicious attacks. This is because many organisations don’t know what data they have, they don’t know where the data is stored, and they don’t know who is touching the data. In short, they don’t know how to protect it.
With all this uncertainty, is it any surprise that the data they have – even if they don’t know they have it – becomes vulnerable to leaks and breaches, be they internal or external? It’s no surprise at all when an organisation has very little idea where their sensitive data is, and who has access to it. This information might be in uncontrolled parts of the network, such as workstations and mailboxes, and it might be classified incorrectly, making it even harder to track down. When a company loses control of information like this, it becomes something of a data mismanagement snowball – growing ever bigger, and ever more problematic. In the modern era, when we’re generating incredible amounts of data on a daily basis, this can be disastrous.

Actions speak louder than words
Many of the challenges with managing data, and protecting it, can be resolved. Security and fraud analytics can protect physical, financial, and intellectual assets from misuse by internal and external threats. Fraud prevention is optimised by efficient data and analytics capabilities, and improved organisational security. What’s more, when data is integrated across an organisation, and everyone buys into this process, fraud across various lines of business, products, and transactions can reveal itself in a clear and singular view. As we see it, action has to be taken in several decisive steps:
1. Provide rapid and accurate visibility of the data landscape
2. Leverage the maximum from existing technologies
3. Understand your risk
4. Reduce the sensitive data footprint
5. Make a positive change to foster a strong data culture
Combined, these steps can transform an organisation’s attitude and approach towards information governance. Bringing in specialists in this field will make this transition a smoother and more productive process, and the results are worth it.
Every problem has a solution
When these steps are taken, common security challenges faced by organisations can be overcome.
For example, if a large organisation is planning a major information governance uplift, one of the challenges they’ll invariably face is to understand what data they hold, where it is and who has access to it. As we’ve already seen, a company with weak data management would struggle to make this work. On the other hand, when the importance of data is acknowledged and experts are brought in to help, they can discover sensitive data across the environment, undertake remediation in the cases where data is found to be in less secure locations, and even classify the data to bring some order to it all. Specialist work like this would significantly reduce the sensitive data footprint, and any remaining sensitive data would be much more visible, but to the right eyes only.
Another challenge might be a lack of visibility of customer and sensitive information held by a regulated organisation. This might lead to data breaches, which will surely set off alarm bells that are loud enough to be heard by regulators. This is another contentious issue that can be solved through specialist input. Email, workstation and internet activity can be analysed, as can files from workstations, shared drives and cloud storage. This analysis might unearth sensitive information in uncontrolled parts of the network, such as the workstations and mailboxes, and vastly increase visibility as a result.
In a situation like this, incorrect data classification can compound the problem. When data is not classified accurately, an organisation will have little idea where their sensitive data is, and who has access to it. Once again, data specialists can help by carrying out organisation-wide data discovery and classification. As a result, the risk of a breach is minimised because of a reduced sensitive data footprint. This is not only good news for the organisation, but for regulators as well. They will have a renewed sense of assurance that the organisation has effective visibility of its information governance risk, and a clear plan towards protecting it.
These two examples show that when it comes to an organisation’s data culture, the weak can become strong. Outside help might be needed to generate the required impetus, but that specialist assistance is out there.
The overall benefits of a strong data culture
Taking control of information within an organisation helps to minimise risk and maximise protection. The chance of suffering reputational and financial damage – damage which might otherwise be irreparable – is decreased. For this to happen, an attitudinal shift has to take place. The importance of data needs to be re-evaluated, and a new respect for sensitive information has to be shared across the organisation. Bringing in specialists in information governance is a huge step towards building a stronger data culture.
When the value of data is fully appreciated, the need to protect it becomes even more apparent. It’s not just for the benefit of the customer. The organisation itself stands to gain from the data it manages.
Business data is a goldmine of information
A greater appreciation of how data is used, and the benefits accruing from it, is something that should be encouraged, and applied. The amount of data we’re generating will continue to increase, and so will the challenges that surround its use and security. Only organisations with a robust and insightful data culture will meet those challenges, and take full advantage of the valuable information at their fingertips.
Contact the Author
Christopher McNaughton
Director | SECMON1
EM christopher.mcnaughton@secmon1.com
PH 0428 183 095
www.SECMON1.com
The Rialto, 525 Collins St. Melbourne
Take control of information in your organisation.
Act now before the data breach storm reaches you. Contact us today.

COVID-19 & Working from home – Mitigate the security risks
As COVID-19 infections increase globally there has been ...
Abhorrent violent material – What you need to know about the Australian Law
If you or your organisation are an internet service prov ...